Cybersecurity requirements across the defense supply chain are tightening as the U.S. Department of Defense rolls out the Cybersecurity Maturity Model Certification (CMMC) program. For organizations handling Controlled Unclassified Information (CUI), CMMC compliance requires significant investments in cybersecurity tools, processes and governance.
While the framework strengthens protection across the Defense Industrial Base (DIB), it also introduces new financial and operational challenges. For security professionals, the focus has shifted to effectively managing compliance costs.
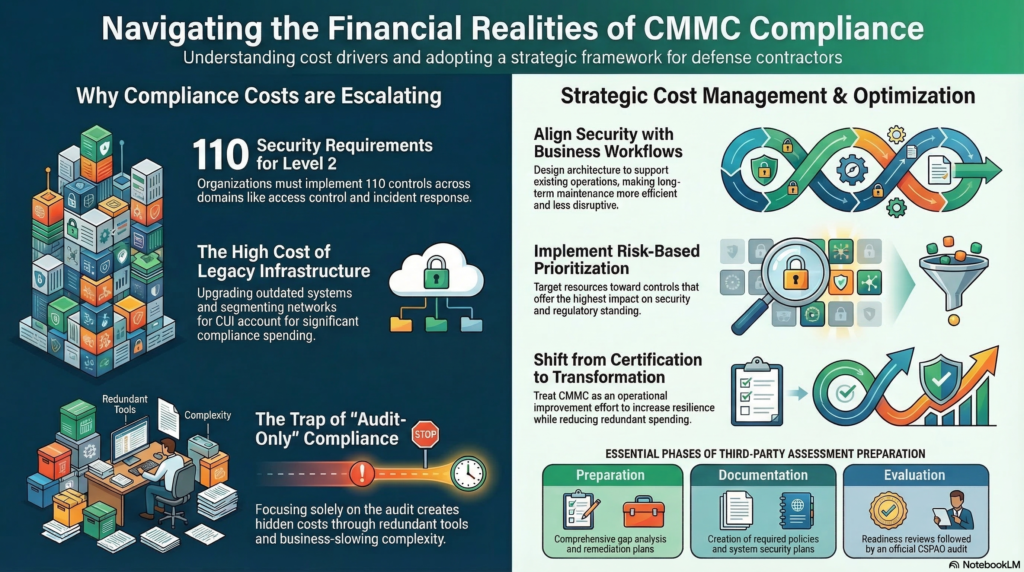
Why CMMC Compliance Costs Are Rising
The CMMC framework enforces consistent cybersecurity standards across organizations supporting the defense supply chain. Here are several factors contributing to the rising cost of compliance.
1. Extensive Security Control Requirements
Organizations pursuing CMMC Level 2 certification must implement all 110 security requirements. These controls span multiple operational domains, including:
- Access control
- Incident response
- System and communications protection
- Audit and accountability
- Risk assessment and configuration management
Implementing these safeguards often requires new cybersecurity technologies, improved monitoring capabilities and comprehensive policy documentation.
2. Infrastructure Modernization
Legacy infrastructure remains one of the most common barriers to achieving CMMC compliance. Many contractors operate systems that do not meet modern cybersecurity standards. Common issues during compliance assessments include:
- Limited centralized logging or monitoring capabilities
- Unencrypted data storage or transmission
- Weak identity and access management practices
- Unclear boundaries around systems handling CUI
Addressing these challenges often requires infrastructure upgrades and network segmentation. These modernization efforts can account for a large share of overall compliance spending.
3. Independent Certification Assessments
Organizations authorized through The Cyber AB, which oversees the CMMC ecosystem, conduct these assessments. Preparing for these third-party evaluations typically involves several stages:
- Conducting a comprehensive gap analysis
- Developing remediation plans for missing controls
- Creating required policies and documentation
- Performing readiness assessments before the official audit
Without structured preparation, contractors risk failing certification assessments and incurring additional costs to address deficiencies.
General Costs of CMMC Compliance
The cost of CMMC compliance for defense contractors varies depending on an organization’s size, operational complexity and current cybersecurity maturity. However, most defense contractors should anticipate a six-figure investment to reach and maintain certification readiness.
These costs typically include consulting services, technical implementation, policy development, readiness reviews and the final assessment conducted by a Certified Third-Party Assessment Organization (C3PAO).
The Hidden Cost of Audit-Only Compliance
One of the most common and expensive mistakes that organizations make is treating CMMC as a simple certification exercise. Some consulting providers focus primarily on helping contractors pass the audit as quickly as possible. While this approach may lead to short-term certification, it can also introduce long-term inefficiencies, including:
- Overlapping or redundant security tools
- Overly complex controls that slow business operations
- Compliance policies disconnected from operational workflows
- Governance structures that are difficult to maintain after certification
These issues often create hidden operational costs that persist long after certification is achieved. For organizations in the defense sector, cybersecurity investments must support both regulatory compliance and operational performance.
A Strategic Approach to Managing CMMC Costs
Contractors seeking to control compliance expenses increasingly adopt a strategy that integrates cybersecurity improvements with broader operational goals. Security professionals typically focus on three guiding principles.
1. Align Security With Business Processes
Cybersecurity controls should support existing workflows rather than disrupt them. When security architecture reflects the organization’s operational model, both implementation and long-term maintenance become more efficient.
2. Implement Risk-Based Prioritization
Not all controls require the same level of investment. A risk-based remediation strategy allows organizations to prioritize resources on controls that deliver the greatest security and compliance impact.
3. Integrate Compliance With Operational Performance
Cybersecurity programs are most sustainable when tied to measurable operational outcomes, such as resilience, efficiency and reduced risk exposure.
A Broader Approach to CMMC Readiness
Organizations such as the Business Transformation Institute (BTI) are helping reshape how defense contractors approach CMMC readiness. Rather than focusing solely on certification milestones, BTI approaches CMMC compliance as part of a broader operational transformation effort. As a CYBER-AB Licensed Training Provider and an authorized C3PAO, its consulting model emphasizes:
- Integrated process development aligned with cybersecurity maturity
- Measuring organizational performance against the customer’s business model
- Creating measurable performance trends that extend beyond certification requirements
While many consulting firms concentrate on achieving specific certifications, BTI focuses on helping organizations improve operational performance while meeting regulatory standards. This approach can help reduce redundant spending while strengthening long-term cybersecurity resilience.
CMMC Compliance For Defense Contractors
CMMC compliance is becoming a defining requirement for participation in the defense supply chain. Organizations that approach compliance strategically — by focusing on efficiency, risk prioritization and operational improvement — can manage costs more effectively while simultaneously strengthening their overall cybersecurity posture.
Devin Partida is a frequent contributor to Brilliance Security Magazine, an industrial tech writer, and the Editor-in-Chief of ReHack.com, a digital magazine for all things technology, big data, cryptocurrency, and more. To read more from Devin, please check out the site.
.
.
Additional Resource
Video Overview
Follow Brilliance Security Magazine on LinkedIn to ensure you receive alerts for the most up-to-date security and cybersecurity news and information. BSM is cited as one of Feedspot’s top 10 cybersecurity magazines.


