Email remains one of the most targeted entry points in cyberattacks. Despite investments in defensive tools, organizations continue to face phishing, business email compromise (BEC) and targeted malware delivered through email. Modern threats are designed to bypass traditional defenses, including secure email gateways (SEGs), underscoring the need for a more adaptive, layered approach.
The Original Purpose of SEGs
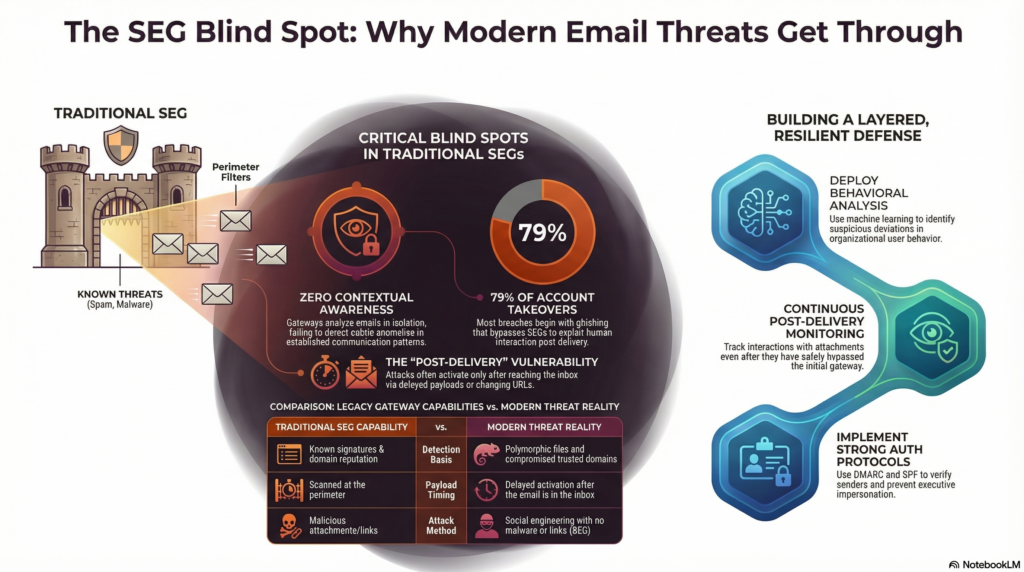
An SEG functions as a perimeter control, inspecting inbound and outbound email traffic before it reaches users. Its primary capabilities include filtering spam, scanning attachments for malware and evaluating URLs using threat intelligence.
This model proved effective against attacks that relied on known indicators, such as malicious file signatures or suspicious domains. Today’s threat landscape, however, emphasizes stealth and legitimacy, reducing the visibility of these traditional markers.
A New Class of Email Threats
Modern campaigns are designed to blend into legitimate communication flows, making them significantly more difficult to detect with traditional tools.
Advanced Phishing
Phishing has evolved beyond generic mass emails. Attackers now use compromised accounts and existing email threads to deliver highly convincing messages. These emails often contain personalized details and realistic requests, increasing the likelihood of user interaction.
Business Email Compromise
BEC remains one of the most financially damaging attack types. By impersonating executives or trusted partners, attackers manipulate recipients into authorizing payments or sharing sensitive data. These emails often contain no malware or suspicious links, allowing them to pass through SEG filters undetected.
Targeted Malware Campaigns
Targeted malware campaigns have evolved to bypass traditional detection by using polymorphic files that change with each delivery, encrypted or password-protected attachments, and delayed payloads that evade sandbox analysis. Attackers often deliver malware via links on trusted platforms, making detection at the gateway even more difficult.
Why SEGs Fall Short
Traditional SEGs provide essential filtering and malware protection, but their design focuses on known threats and isolated email analysis. As attackers increasingly rely on deception, trust exploitation and rapidly changing tactics, these gateways face inherent limitations. Understanding these gaps is key to strengthening email security strategy.
Limited Detection Models
SEGs rely heavily on known indicators like signatures and domain reputation. Modern threats often avoid these markers, rendering traditional filtering techniques ineffective.
Lack of Contextual Awareness
Email gateways analyze messages in isolation and lack insight into user behavior, communication patterns and organizational relationships. This limitation makes it difficult to identify subtle anomalies, such as unusual financial requests from familiar contacts.
Difficulty Interpreting Social Engineering
Social engineering exploits human behavior rather than relying on malicious code. Factors like trust, cognitive bias and limited training drive many breaches. SEGs cannot assess intent or detect manipulation, highlighting the need for defenses that combine human awareness with technology.
Exposure to Rapidly Evolving Threats
Attackers frequently rotate infrastructure, including newly created domains and short-lived payloads. This speed creates gaps between threat emergence and detection updates, increasing exposure risk.
The Rise of Post-Delivery Attacks
Many modern threats only become active after an email reaches the inbox. This includes links that change behavior over time and documents that, once opened, retrieve malicious content. Because traditional SEGs focus on predelivery inspection, these multistage attacks can pass through undetected, leaving users vulnerable even after messages appear safe.
Human interaction often completes these attacks. Notably, 79% of account takeovers begin with phishing, showing that post-delivery threats often rely on users taking action, whether by clicking a link, opening a document or following instructions.
Similar to how marketers use advanced tracking in email service providers (ESP) to monitor engagement and campaign performance, security professionals can use similar post-delivery visibility to observe how users interact with links, attachments and documents. Integrating these insights with threat intelligence briefings from ESPs helps identify unusual behavior or anomalies early, improving the detection of threats that operate quietly within trusted communications.
Building a More Resilient Email Security Strategy
Strengthening email defenses requires a layered approach that goes beyond traditional SEGs. Key strategies include:
- Advanced threat detection: Use behavioral analysis and machine learning to identify unusual or suspicious anomalies in user behavior and communication patterns across the organization.
- Continuous monitoring: Track interactions with attachments and links to detect evolving threats that appear after delivery and respond before damage occurs.
- Strong authentication protocols: Use Domain-based Message Authentication, Reporting, and Conformance and Sender Policy Framework to verify senders and prevent spoofing.
- User awareness: Human mistakes account for many security breaches. Provide training and phishing simulations to help users spot suspicious emails. Regular practice reinforces vigilance and reduces risk.
Closing the Visibility Gap in Modern Email Security
SEGs remain important but have limited visibility into sophisticated threats that exploit trust and timing. A layered approach combining SEG protection, context-aware detection, strong authentication, and user-focused defenses helps organizations reduce exposure and stay ahead of evolving email attacks.
Devin Partida is a frequent contributor to Brilliance Security Magazine, an industrial tech writer, and the Editor-in-Chief of ReHack.com, a digital magazine for all things technology, big data, cryptocurrency, and more. To read more from Devin, please check out the site.
.
.
Additional Resource
Video Overview
Follow Brilliance Security Magazine on LinkedIn to ensure you receive alerts for the most up-to-date security and cybersecurity news and information. BSM is cited as one of Feedspot’s top 10 cybersecurity magazines.

