Executive protection has always been a physical discipline. Motorcades, residential security, and advance teams. But the threats that create the most physical risk today often start with something nobody in the security detail can see: a data broker profile, an old Strava route, or a tagged photo on a teenager’s Instagram account.
The uncomfortable truth for security teams is that digital exposure and physical risk are no longer separate problems. They feed each other. And the place where they converge most dangerously is the executive’s family.
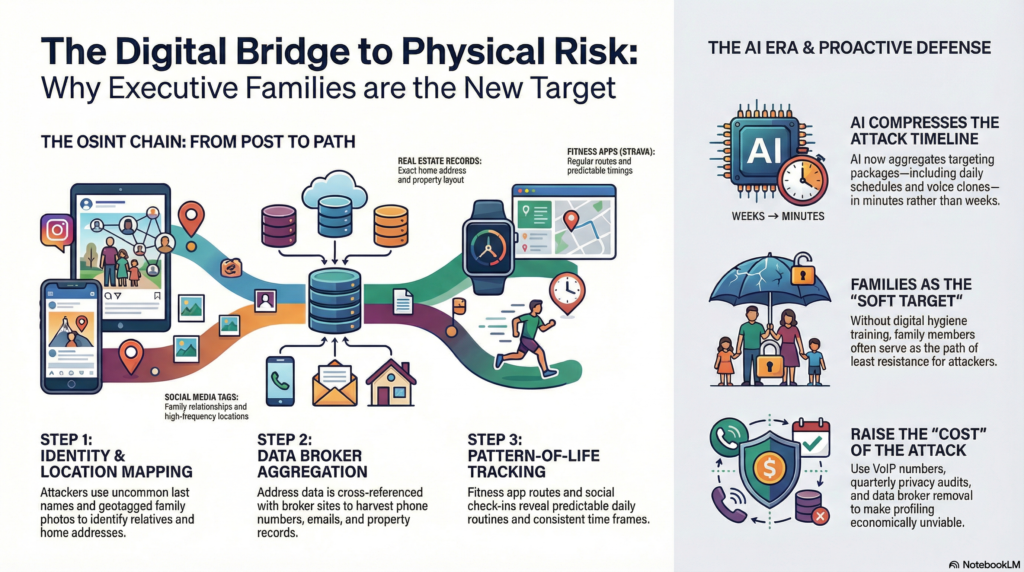
The OSINT chain that leads to the front door
A motivated attacker doesn’t need to “hack” anything. Open-source intelligence gathering against a family follows a predictable sequence, and it’s disturbingly simple.
The first step is to find a name. If the executive’s spouse or child share an uncommon last name, finding their social media presence can take seconds. From that point on, one geotagged photo or one check-in at a restaurant near the home will narrow down the area significantly.
Next, cross-reference that with property records or real estate listings, and you now have an address. Enter the address into a data broker website, and you will get a profile on each individual who is associated with that address, including phone number(s), e-mail addresses, and often a list of relatives.
Finally, add in fitness app data. Fitness apps like Strava and others track routes that most often start and stop at the same location. While privacy settings are enabled, activity data is still leaked through group challenges, shared segments, or followers. This data provides what the physical security community is worried about: pattern-of-life. Regular routes, consistent time frames, and predictable locations.
None of these steps requires a breach or technical sophistication. All of this data is publicly available, spread out across many different websites and platforms, and just waiting to be pieced together.

Why families are the softer target
Executives working in high-risk environments have a general understanding of the basics. They have received training or at least some form of digital hygiene.
Family members don’t receive the same level of education. For example, a spouse’s use of LinkedIn may be similar to that of many users of Facebook, i.e., sharing vacation photos, tagging the executive, and posting from the front porch. A college-aged child may also post on a public Venmo account showing their transactions and contacts. These aren’t security failures. They’re just people living online without context about how that information connects them to their family and the organizations they work for.
When the executive’s digital footprint is clean, the family becomes the path of least resistance. And the information collected from family members often maps directly back to the executive, the home, and the organization.
AI is compressing the timeline
This kind of profiling used to take days or weeks of manual research. AI is now able to complete this research in mere minutes.
AI models are now being trained on aggregating public data sources and creating a “targeting package” consisting of; home address, daily schedule, family members, associated accounts, and known associates.
Another area where AI is providing an additional attack vector is deep fake voice cloning. If an attacker has obtained enough audio from a family member’s social media, they can create a very realistic voice call. A panicked family member asks for money via wire transfer. The spouse calls the executive assistant to ask if he can change his schedule. These types of attacks prey upon the trust-based relationship that is virtually unverifiable at the time of the attack.
The speed matters. When profiling is fast and cheap, the number of people who can be targeted goes up. Families that might not have been worth the effort a few years ago are now well within reach.
Bridging the gap between cyber and physical teams
In many organizations, physical security and digital privacy are managed by separate departments, under different budgets and reporting channels. That’s a problem when the threat itself doesn’t recognize those boundaries. A CISO can manage the credential monitoring, breach alerts, etc., while a corporate security director manages the travel risks and residential security for executives. However, neither of these individuals will likely consider that the executive’s wife has reused a compromised password on her home security system, or that the executive’s teenage child has posted information publicly on their social media accounts, creating a “pattern-of-life” trail.
Closing this gap starts with a shared understanding: digital exposure creates physical risk, and family members are the most common bridge between the two. That means physical security teams need visibility into the family’s digital footprint, and cyber teams need to understand which exposures translate into real-world targeting opportunities.
Practical steps that don’t require a new budget
Family protection doesn’t need to be an additional or costly program. A few practical steps will help.
Look at family members’ social media for posts with tagged/explicitly stated locations, lists of who follows your family, and posts where another party is tagged. Set up Multi-Factor Authentication using Authenticators for all family members. Use VoIP phone numbers for sign-ups and reservation confirmations as opposed to using personal cell phone numbers. Remove your family’s home address, year of graduation, and relationship to other family members from data broker sites. Check your fitness app’s Privacy Settings every quarter, not just when you set it up.
These measures work because adversaries are constrained by the same economics as everyone else. Time, effort, and return on investment matter to them, too. If you make a family harder to profile than the next target, most threats move on.
The organizations getting this right treat family digital exposure as a standing item in their threat assessments, not a one-time project. Because the data regenerates, the platforms change, and new exposures appear constantly.
When digital and physical security teams share that responsibility, the gap between executive protection and family exposure starts to narrow.
Ben Skean is the Director of Cyber Threat Intelligence at 360 Privacy, where he leads intelligence, investigations, and threat analysis supporting enterprise and high-risk clients. He oversees CTI strategy, analyst tradecraft, investigation frameworks, and the integration of intelligence workflows across monitoring and client services. He also drives standardized OSINT methodologies, PII exposure alerting, and secure research practices to ensure actionable, compliant intelligence outcomes.
Ben joined 360 Privacy in 2024 after nearly a decade as a digital targeter with the National Security Agency, embedded with U.S. Army Special Operations. He deployed overseas three times, focusing on hostile threat actors in the Middle East, target development, intelligence fusion, and security implementation in austere environments.
Additional Resources
Video Overview
Infographic
Follow Brilliance Security Magazine on LinkedIn to ensure you receive alerts for the most up-to-date security and cybersecurity news and information. BSM is cited as one of Feedspot’s top 10 cybersecurity magazines.


