Why identity assurance is replacing awareness training and legacy MFA as the real frontline of cyber defense
A TokenCore announcement led to a deeper question: if organizations have spent years investing in training, MFA, and detection, why do identity-driven attacks still work so well?
A recent Business Wire press release announcing that Token had evolved into TokenCore and broadened its vision for cryptographic identity assurance piqued my interest. What began as a routine look at a company’s public statement quickly turned into a deeper research exercise into a much larger problem: why identity-driven breaches keep succeeding despite years of investment in training, MFA, and increasingly sophisticated security stacks.
This article is the result of that research. It examines why the “human firewall” model is breaking down, why many legacy authentication controls are no longer sufficient against modern phishing and adversary-in-the-middle attacks, and why identity assurance is emerging as a more meaningful standard than traditional identity management. TokenCore is an essential part of that story, but the larger issue is one facing the entire cybersecurity industry.
Security keeps expanding, but trust keeps failing
Cybersecurity has a way of looking stronger than it is.
Organizations add tools, improve visibility, expand telemetry, and refresh awareness training. The stack gets bigger. The dashboards get better. The language gets more polished. And yet attackers keep getting in.
In many cases, they are not smashing through hardened defenses. They are logging in with stolen credentials, hijacked sessions, or relayed authentication flows that make them appear legitimate.
That is the core problem. Much of the industry still treats identity compromise as something to detect after the fact, even though it has increasingly become the opening move. If the wrong person is accepted as the right user, the rest of the security stack is already working from a false assumption.
That is why identity management is no longer enough. What matters now is identity assurance: proving that the person requesting access is the actual, authorized human being at the moment trust is granted.
Too much of modern security is built to observe compromise
A great deal of today’s security infrastructure is designed to watch attacks unfold rather than stop them at the point of entry.
That is not useless. Visibility matters. Detection matters. Forensics matter. But none of those functions prevent an attacker from gaining access if the authentication event itself is trusted too easily.
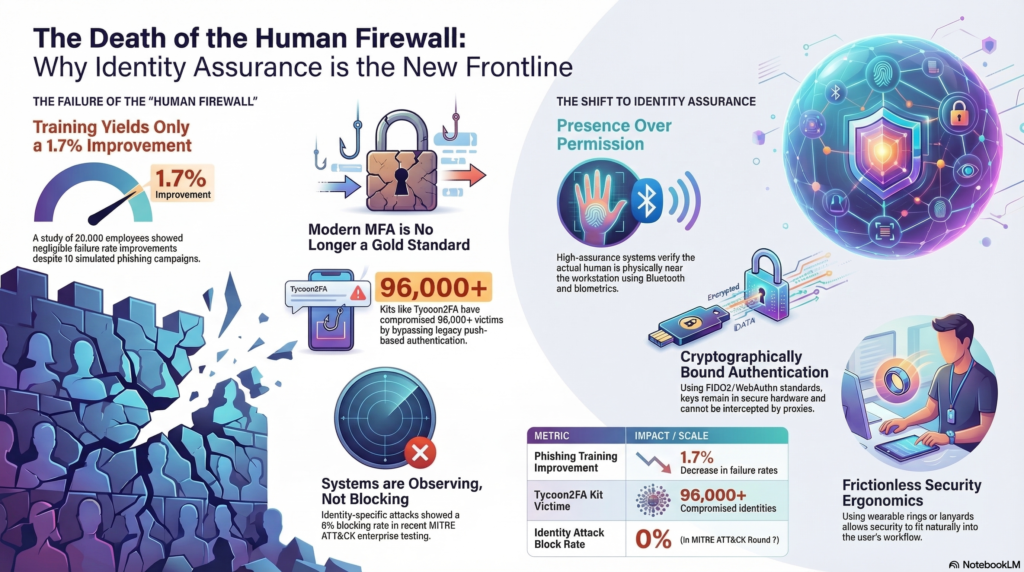
According to analysis cited in the source material behind this article, identity-specific attacks showed a 0% blocking rate in the MITRE ATT&CK Enterprise Round 7 context [2]. However one interprets comparative testing, the implication is difficult to ignore. When the attack begins with what looks like a legitimate login, too many products become spectators.
They can flag anomalies later. They can build a detailed incident timeline. They can help explain what happened. But they often do not stop the login.
That is the strategic gap. Security teams have spent years investing in seeing more. Increasingly, they need systems that trust less.
The “human firewall” was always a weak premise
For years, the industry has leaned on a familiar phrase: the human firewall.
It sounds responsible, even empowering. Train users well enough and often enough, and they become a dependable line of defense against phishing, fraud, and social engineering.
The problem is that this idea asks too much of people and too little of systems.
Users are busy. They work under pressure. They multitask. They respond to urgency, authority, and familiarity because that is how human beings operate. Attackers understand this and design campaigns around it.
Awareness training still has value. It can improve reporting habits and reduce some obvious mistakes. But it does not turn ordinary employees into reliable security controls under adversarial conditions.
The data cited by Token reinforces that point. A UC San Diego Health study involving 20,000 employees found that after ten simulated phishing campaigns over eight months, along with mandatory training, the improvement in failure rates was just 1.7% [3].
That is not an indictment of users. It is an indictment of the model. A mature security program should not depend on employees making flawless security judgments in moments specifically engineered to defeat judgment.
MFA mattered, but attackers adjusted
Multi-factor authentication was supposed to solve the password problem. In many environments, it still significantly reduces risk. But that does not mean it has held its original position as the gold standard.
Attackers adapted. Real-time phishing proxies, adversary-in-the-middle kits, push fatigue attacks, and session hijacking have exposed the weakness in many legacy MFA deployments: they still rely on secrets, prompts, or approvals that can be intercepted, relayed, or manipulated.
The Tycoon2FA kit reportedly compromised more than 96,000 victims [2]. More important than the number is what it represents. Capabilities that once required meaningful expertise are becoming easier to package, scale, and deploy.
That changes the question defenders should be asking. It is no longer enough to ask whether the user supplied the correct factor. The better question is whether the authentication event itself can be trusted.
This is where hardware-backed, cryptographically bound authentication becomes more compelling. With standards such as FIDO2 and WebAuthn, authentication can be tied to the legitimate domain and anchored to a private key that remains in secure hardware [3][5]. If the destination is not genuine, the transaction does not complete.
That is a much stronger proposition than asking a user to recognize a convincing fake in real time.
The real issue is presence
The deeper problem is not whether the right credential was presented. It is whether the right person is actually there.
That is why the TokenCore story is interesting beyond the company announcement itself. The material behind this article describes an approach built around hardware-enforced biometric verification and proximity-aware authentication tied to a physically present user [5].
That matters because presence is harder to fake than permission.
Traditional authentication systems care primarily about whether the required information was supplied. They often care far less about whether the session is being relayed, whether the request originates far from the user, or whether the person at the endpoint is actually the authorized individual. If the factors line up, access is granted.
A proximity-based approach changes that logic. According to the company’s website, TokenCore uses Bluetooth Low Energy to help ensure the authorized user is physically near the workstation [5]. The system can also lock when the user walks away, require fresh biometric proof for sensitive actions, and treat trust as something that must be continuously supported rather than granted once and assumed thereafter [3].
That is the shift. Authentication stops being a one-time hurdle and becomes ongoing proof of authorized human presence.
In a threat environment shaped by cloud identity, remote access, session theft, and AI-assisted impersonation, that is not a fringe idea. It is where stronger security appears to be heading.
Security only works if people will actually live with it
Even strong controls fail if users hate them.
That is one of the industry’s more stubborn blind spots. Security teams often focus on technical rigor, while users focus on speed and convenience. When those priorities collide, workarounds follow.
That is why usability matters. A control can be sound in theory and still fail in practice if it is too disruptive, awkward, or easy to resent.
The multiple TokenCore form factors reflect this reality: a wearable ring, a lanyard-style device, and a portable USB-C biometric stick, all centered on fingerprint verification [5].
Those are not trivial packaging decisions. They point to an important truth. Different work environments require different kinds of security ergonomics. A wearable may suit clinical or industrial settings where repeated login friction slows operations. A lanyard may fit badge-oriented workplaces. A portable device may better suit administrators or mobile professionals.
The broader lesson is simple. Security becomes more durable when the secure action fits naturally into the user’s day.
The old “human firewall” concept failed because it expected users to compensate for weak systems. Better identity assurance does the opposite. It builds stronger systems around ordinary human behavior.
Identity is now the front line
For years, the center of gravity in cybersecurity was the network, the endpoint, or the data store. Those layers still matter, but identity has become the more decisive battleground.
That shift changes everything. Identity is no longer just an administrative function. It is the mechanism through which trust is granted, privilege is expanded, and defenses are bypassed.
That is what made the Token-to-TokenCore announcement worth a closer look. It was not merely a rebrand. It reflected a broader realization that the old trust model is losing credibility.
Passwords are weak. Relayable MFA is vulnerable. Awareness training has limited upside. Detection is inherently reactive. None of that means existing controls no longer matter. It means they cannot compensate forever for weak identity assurance.
Access must be tied more directly to the verified, present, authorized human being. Not just to a password. Not just to a device. Not just to a push notification someone can approve at the wrong moment.
To a person.
The comfortable myth has run its course
The phrase “human firewall” survives because it is comforting. It suggests that with enough training, enough reminders, and enough vigilance, organizations can solve a problem rooted in system trust.
But comfort is not security.
Modern attacks are designed to exploit human judgment, reuse trusted workflows, and slip through authentication models built for a simpler era. That does not mean users have failed. It means the model around them has.
Organizations can keep layering factors onto weak foundations, or they can confront the harder question: how do you prove the right human is actually present before trust is extended?
That is where identity assurance enters the conversation, not as a slogan, but as a necessary evolution.
The human firewall is dead. The next phase of security begins when the industry stops pretending otherwise.
Sources
- Token | Biometric Identity Assurance | Enterprise Security, tokencore.com
- Kevin Surace, “The Cybersecurity Industry Has a Terrifying Problem — and Most CISOs Are Not Scared Enough,” Token Blog
- Paradigm Shift Analysis: “The Paradigm Shift in Identity Assurance: A Comprehensive Analysis of Token’s Biometric Cryptography”
- “Token Evolves into TokenCore, Expanding Its Vision for Cryptographic Identity Assurance,” Business Wire press release
- TokenCore Biometric Hardware Technical Specifications, “All notes 3/20/2026”
Additional Resource
Video Overview
Steven Bowcut is the Editor-in-Chief of Brilliance Security Magazine and host of the BSM Podcast. He has spent years covering cybersecurity and physical security, focusing on the technologies, strategies, and leadership insights that matter most to security practitioners and decision-makers. Through the magazine and podcast, Steven brings readers and listeners practical content with industry leaders, innovators, and experts shaping the future of security. Follow and connect with Steve on Instagram and LinkedIn.


