Mobile apps have become an integral part of our lives, and we use them for everything from communication to shopping and banking. However, with the increasing use of mobile apps comes the risk of runtime attacks that could manipulate the device environment. Runtime attacks refer to attacks occurring while an app runs on a device. Threat actors employ these attack methods to steal personal data, manipulate app functionality, or take control of the device.
It is crucial for mobile apps – especially fintech apps – to be built with effective defenses against runtime attacks. Here are some reasons why:
- Protect user data: Fintech apps often contain sensitive user data, such as passwords, credit card information, and personal identification details. Hackers can easily steal and use this data for malicious purposes if an app is vulnerable to runtime attacks. Good defenses against runtime attacks can guard this data and protect users’ personal information.
- Maintain app integrity: Threat actors use runtime attacks to manipulate an app’s functionality or change its operation. This can lead to a poor user experience or, worse, cause the app to malfunction altogether. Defenses against runtime attacks can prevent these issues and maintain the app’s integrity.
- Prevent device takeover: In some cases, runtime attacks can give hackers complete control over a user’s device. Digital adversaries will then use this control to spy on the user, install malware, or steal more data. Proper defenses against runtime attacks can prevent these attacks and keep the user’s device secure.
- Build user trust: Mobile app users are becoming increasingly aware of the risks of runtime attacks, and they expect app developers to take steps to protect their data and devices. Building adequate defenses against runtime attacks can help build user trust and increase user engagement with an app.
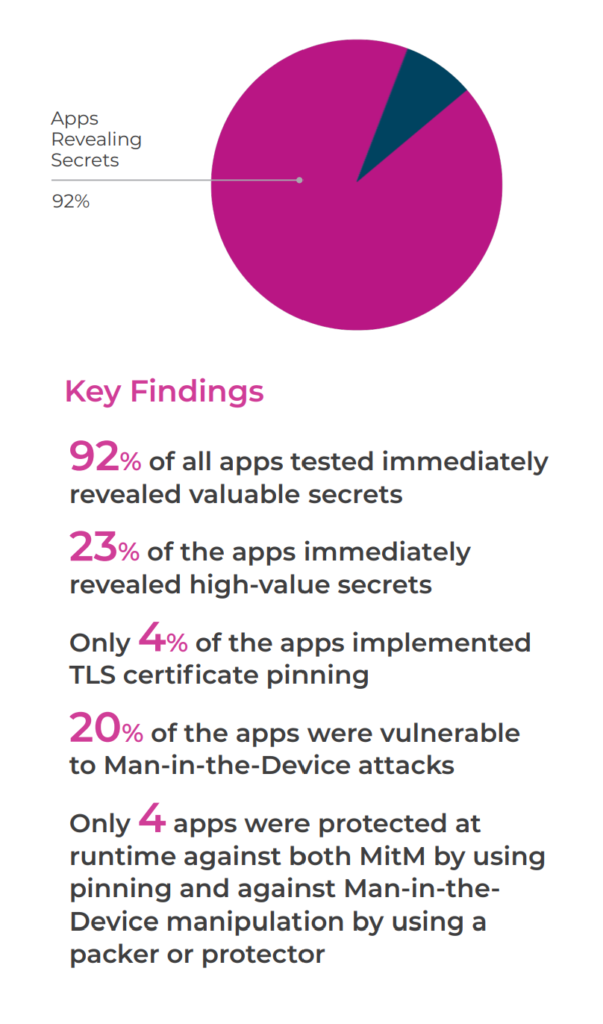
A recent study by the Approov Mobile Threat Lab revealed that a staggering 92% of the 650 most prominent financial services applications on the Google Play Store are exposed to severe security vulnerabilities. The report, titled ‘Mobile App Security Report – Exposing the Security Vulnerabilities of Top Finance Apps’, was generated after downloading, decoding, and scanning 200 financial services apps in four key countries – including the U.S., UK, France, and Germany. The findings of this report are highly concerning, given the private nature of financial information handled by such apps.
Scans revealed that only a tiny fraction (5%) of the studied applications had effective protective measures against runtime attacks that manipulated the device environment. Only four percent were adequately safeguarded from Man-in-the-Middle (MitM) attacks. Besides revealing confidential information, security scans further identified two critical attack surfaces during runtime that hackers could exploit to acquire API keys.
“This research shows hardcoding sensitive data in mobile apps is widespread and a massive problem since secrets can easily be extracted. A simple automated scan can show any threat actor how well protected apps are at runtime. Unfortunately, financial apps fall short,” Approov CEO Ted Miracco said. Miracco asked, “Have we all unknowingly become beta-testers for financial services apps? Is this putting our personal finances at risk?”
Other findings:
- None of the 650 apps “ticked all the boxes” regarding the three attack surfaces investigated. All failed in at least one category.
- Only four apps had runtime protection against channel MitM attacks and “man-in-the-device.” All were payment and transfer apps, and none were in the U.S.
- In general, apps deployed in Europe were better protected than apps available only in the U.S. for immediate secret exposure and runtime protections. This additional protection may be due to stricter privacy rules in Europe and more focus on security.
- Crypto apps were more likely to leak sensitive secrets, as 36% immediately offered highly sensitive secrets when scanned.
- Only 18% of personal finance apps leaked sensitive information, possibly because they depend less on sensitive APIs.
- For Man-in-the-Device attacks, traditional banks are twice as likely to be well protected over other sectors reflecting the use of packers and protectors to guard against runtime manipulation.
The results of the Approov Mobile Threat Lab’s study are concerning, and it is clear that many mobile applications lack adequate protection against runtime attacks. These inadequate defenses mean that users’ data may be at risk from malicious actors who can exploit these vulnerabilities to access confidential information or even take control of a user’s device.
App developers must ensure their products have robust security measures in place to build trust with customers by protecting them from potential threats. By implementing effective defenses against common attack surfaces such as MitM attacks and Man-in-the-Device attacks, financial services apps will help protect customer data while providing peace of mind.
Steven Bowcut is the Editor-in-Chief of Brilliance Security Magazine and host of the BSM Podcast. He has spent years covering cybersecurity and physical security, focusing on the technologies, strategies, and leadership insights that matter most to security practitioners and decision-makers. Through the magazine and podcast, Steven brings readers and listeners practical content with industry leaders, innovators, and experts shaping the future of security. Follow and connect with Steve on Instagram and LinkedIn.