The future of security operations is not just smarter AI. It is a smarter design. Start with the people doing the work.
By Peter R. Kelley
Dubai-based Secure.com has just released “Designing Security Workflows Humans Don’t Hate” based on data compiled from organizations across more than 30 countries.
Secure.com CEO Uzair Gadit advocates for human-first security workflows, designed around how people actually work, not how tools were built. The human-first approach surfaces what is relevant, removes friction from the right actions, and puts human judgment where it is needed most, instead of everywhere.
He said: “Most security workflows treat people like machines. They expect analysts to process hundreds of alerts, jump between tools, and make fast decisions under pressure all day, every day. When security workflows fight your team instead of supporting them, people stop following them and that’s when the real risk begins.”
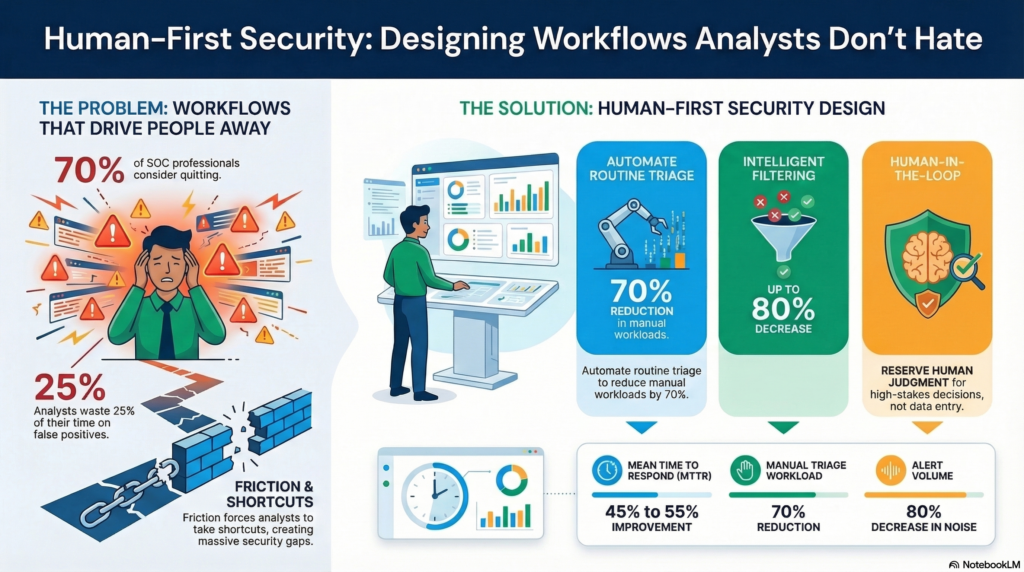
Security Workflows That Drive People Away: Security is not broken, it’s overworked. Most security workflows treat people like machines. They expect analysts to process hundreds of alerts, jump between tools, and make fast decisions under pressure all day, every day. Over 70% of SOC professionals say they have considered quitting due to stress and unmanageable alert volumes. That is not a sign of weak teams. It is a sign of broken workflows.
The Visibility Trap: More data does not equal more security. When everything is flagged as urgent, teams stop trusting their tools. Critical threats get buried under noise. According to a Trend Micro survey, 51% of SOC teams feel overwhelmed by alert volume, and analysts spend over 25% of their time handling false positives alone. When everything looks the same level of urgency, nothing gets treated urgently.
Friction is a Security Risk: When a workflow is slow, confusing, or repetitive, people find shortcuts. Those shortcuts are not laziness, but survival. One analyst put it plainly in an online security forum: “I hate touching the SIEM because I feel like I don’t know how to do any meaningful work there.” When the tool becomes an obstacle, people route around it. And when they route around it, the gaps widen.
What Human-First Security Design Actually Looks Like
First, it prioritizes signal over volume:
- Risk-based alert scoring, context enrichment, and behavioral correlation are the tools that separate real threats from background noise.
- Organizations that have adopted intelligent filtering report up to 80% fewer alerts reaching human analysts without sacrificing detection quality.
It builds security into the tools people already use:
- A new dashboard is another hill to climb. Security works best when it lives inside the tools people already use, whether that is Slack, Jira, or email.
- When analysts can review an escalation, approve a response, and close a case without leaving the tool they are already in, the friction drops.
It gives teams context, not just tasks:
- Telling a team “fix this vulnerability” without showing the risk, the blast radius, or the business impact is a fast path to deprioritization. Context turns a ticket into a decision.
- When an alert shows the affected asset, the threat classification, what happened before and after, and what the recommended action is, analysts can move quickly and confidently.
The Human-in-the-Loop Problem (And How to Solve For It):
Here’s where automation belongs:
- Routine correlation, evidence collection, ticket routing, and follow-up tasks are where automation earns its keep. These are not decisions that need human judgment. They are tasks that drain it.
- Organizations that automate these workflows report a 45 to 55% improvement in Mean Time to Respond (MTTR) and a 70% reduction in manual triage workload. That time goes back to analysts so they can do the work that actually requires them.
Here’s where humans belong:
- High-stakes approvals, escalation calls, and risk tradeoffs need real judgment. Smart workflow design protects human attention for exactly those moments.
- When automation handles the triage, enrichment, and routing, analysts can focus their energy on the decisions that could determine whether a breach happens or not.
Cybersecurity advances through a straightforward idea: governance and usability are not opposites. Every action is traceable. Every decision is explainable. Every workflow is designed so analysts spend their time on what matters, not on chasing noise.
For example, Secure.com’s Digital Teammates work where analysts already are. They integrate with 200+ existing tools including SIEMs, EDRs, cloud platforms (AWS, Azure, GCP), ticketing systems (Jira, ServiceNow), and collaboration tools (Slack, Teams), surfacing pre-written investigation summaries, flagging what needs a human decision, and handling the rest automatically under full audit trail. This yields:
- Automated triage and enrichment: Digital Teammates filter repetitive alerts and investigate low-severity events automatically, reducing manual triage workload by 70%.
- Unified context: Instead of switching between five tools, analysts see everything they need in one view, including asset data, threat intelligence, and related incidents.
- Drag-and-drop workflow builder: Teams can build and update response playbooks without writing a single line of code.
- Human-in-the-loop by design: High-impact Digital Teammate actions require analyst approval before execution. Low-risk, routine tasks are automated with full audit logging. Every step is logged, reversible, and auditable.
Gadit stresses that Security doesn’t fail because defenders stop trying. It fails when tools and workflows make the job harder than it should be.
“People who trust their workflows use them. When they use them, the security posture is real and not just something that looks good on a compliance report. The future of security operations is not just smarter AI. It is a smarter design. And that starts with the people doing the work.”
Gadit’s Key Takeaways
- Bypassed workflows aren’t just an inconvenience; they’re a security risk. When security processes and workflows ask too much from people without giving back, human nature steps in and teams find workarounds. Those workarounds are where the real security gaps live.
- More alerts doesn’t equate to more security. SOCs process thousands of alerts a day, and most go uninvestigated. Prioritized, context-rich signals beat high-volume noise every time.
- Friction’s a design problem, not a people problem. If analysts are routing around their tools, the tools are the issue. With intelligent workflow design, the secure choice is also the obvious one.
- Automation should handle what’s repetitive so humans can handle what’s meaningful. Triage, enrichment, and routing do not need human judgment. High-stakes decisions do. Smart design separates the two.
- Security works best when it lives inside the tools the team already uses. Every new dashboard is another hill to climb. When security fits into existing workflows, adoption follows naturally.
For guidance and context, Secure.com offers working examples of how workflows built for humans actually work.
Additional Resource
Video Overview
Follow Brilliance Security Magazine on LinkedIn to ensure you receive alerts for the most up-to-date security and cybersecurity news and information. BSM is cited as one of Feedspot’s top 10 cybersecurity magazines.

