Preparing a formal CMMC assessment involves demonstrating that your security operations already function in a disciplined, repeatable and measurable way. Rather than striving for the most documentation, organizations should follow a clearly defined CMMC process flow and shape environments to naturally reflect cybersecurity maturity.
Move Beyond Checklists and Into Operational Proof
Cyber scams are increasing in frequency and sophistication, costing businesses significant financial losses. That’s why strengthening your security posture and proactively protecting your systems is essential.
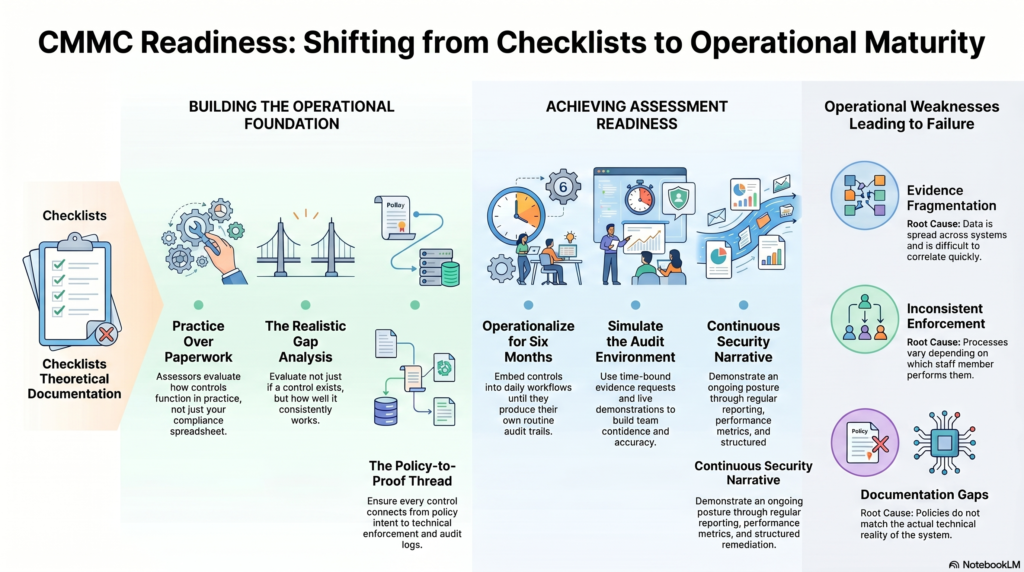
It’s tempting to anchor your preparation around control checklists, especially given the structure of NIST SP 800-171. But assessors are evaluating your environment, not your spreadsheet. They want to see how controls function in practice, how consistently you apply them and whether they hold up under real-world conditions.
A well-defined CMMC process flow ensures that every layer connects logically. Policies establish intent, procedures define execution, systems enforce behavior and audit logs provide evidence. If one of those layers is weak or disconnected, the entire structure becomes unreliable from an assessor’s perspective.
This is where mature organizations distinguish themselves. Assessors look for controls that are observable, measurable and repeatable.
Conduct a Gap Analysis That Reflects Reality
A meaningful gap analysis goes well beyond identifying missing controls. It tests whether your current implementation can withstand scrutiny. That means evaluating not just whether something exists, but how well it works and how easily it can be proven.
NeoSystems provides specialized CMMC gap analysis and audit preparation to government contractors to align with industry standards. They work with businesses to help them achieve and sustain CMMC compliance.
A strong gap analysis typically uncovers issues like:
- Controls that exist but lack consistent enforcement
- Evidence that is technically available but difficult to retrieve
- Processes that vary depending on who performs them
- Documentation that does not fully match operational reality
These are the kinds of weaknesses that don’t show up in basic assessments but become obvious during a formal review.
Build an Evidence Model That Holds Up Under Pressure
Evidence is where preparation becomes tangible. It’s also where many organizations struggle. They may have the right controls yet lack cohesion. Assessors expect to follow a clear thread from policy to execution to proof.
A structured CMMC compliance guide ensures that each control is supported by multiple layers of evidence that reinforce one another. For example, access controls should be documented in policy and reflected in provisioning workflows, enforced through technical controls and visible in system audit logs.
According to KPMG, one of the most common issues is fragmentation. Evidence exists, but it’s spread across systems, inconsistently maintained or difficult to correlate quickly. That lack of cohesion can create doubt, even when the underlying controls are sound. To strengthen your evidence model, organizations often focus on:
- Centralizing documentation and artifacts in a controlled repository
- Standardizing naming conventions and version control
- Ensuring audit logs are retained, searchable and time-synchronized
- Linking evidence directly to specific control requirements
When done well, this creates a narrative that is easy for assessors to follow and trust.
Operationalize Controls Until They Are Routine
Implementation is only the starting point. True readiness comes from operationalization, when controls are embedded into everyday workflows and function without constant oversight. Most businesses should allow around six months to prepare.
This is where automation becomes particularly valuable. Booz Allen Hamilton frequently highlights that automation is essential for maintaining consistency at scale. Whether it’s automated patching, continuous monitoring or alert-driven response workflows, these systems reduce variability and generate reliable evidence over time. In practice, operational maturity often includes:
- Continuous monitoring through SIEM or similar platforms
- Automated enforcement of configuration baselines
- Regular, system-driven access reviews
- Incident response processes that are both documented and consistently executed
When controls operate this way, they produce their own audit trail, making assessment preparation far less burdensome.
Align People With Processes and Technology
Even in highly automated environments, people remain a critical factor. Assessors will engage directly with your team, and their ability to clearly explain processes and responsibilities is crucial for the outcome.
Clear ownership and accountability are essential CMMC compliance steps that should not be left implicit. Organizations often underestimate how quickly inconsistencies in staff responses can signal deeper operational issues.
Teams supported by Neosystems frequently address this by formalizing control ownership and ensuring that each individual understands both their operational role and how it relates to compliance requirements. This alignment creates consistency in execution and communication during the assessment itself.
Simulate the Assessment Environment
Organizations working with Deloitte often simulate real-world attack or failure scenarios to validate control effectiveness. Mock assessments are one of the most effective ways to refine readiness, but only if they are conducted realistically. A casual review of documentation isn’t enough. The process should mirror the pressure and structure of an actual audit.
Organizations that invest in multiple simulation cycles tend to see significant improvement. Deloitte has observed that repeated exposure to assessment conditions helps teams become faster, more accurate and more confident in presenting evidence. A strong simulation typically involves:
- Time-bound evidence requests to test retrieval speed
- Live demonstrations of system controls
- Direct questioning of staff across different roles
- Identification and correction of inconsistencies in real time
By the final iteration, the process should feel familiar rather than disruptive.
Keep Documentation Precise and Aligned
Documentation should reflect reality, not aspiration. Overly complex or outdated documentation can create more risk than failure, especially if it contradicts actual practices.
A well-aligned CMMC process flow ensures that policies, procedures and technical controls all reinforce each other. When an assessor reviews your documentation, they should see a consistent story that aligns with what they observe in your systems and what your team tells them.
Clarity is more important than volume. Concise, accurate documentation is far more effective than lengthy material that’s rarely referenced or inconsistently applied.
Treat Continuous Monitoring as an Ongoing Narrative
Recognize that CMMC is not about a single point in time. It reflects your organization’s ability to maintain a continuous security posture.
Firms like KPMG emphasize the importance of demonstrating this continuity through regular reporting, defined performance metrics and structured remediation processes. These elements show that your organization is capable of detecting issues and managing and resolving them in a disciplined way.
Frequently Asked Questions
Learn more about CMMC compliance.
How long does it typically take to prepare for a CMMC assessment?
Preparation timelines vary depending on factors such as the level of certification being pursued and the readiness of your cybersecurity practices. Those with established security operations and a defined CMMC process flow can move faster than those building controls from scratch.
What is the most common reason organizations fail a CMMC assessment?
Failure usually comes down to weak or inconsistent evidence. Even when controls exist, poor documentation, fragmented audit logs or unclear ownership can undermine a strong CMMC compliance guide and approach during assessor review.
Do you need external support to achieve CMMC readiness?
Not always, but many organizations benefit from expert validation. Firms help refine CMMC compliance steps, identify blind spots and simulate real assessment conditions effectively.
When Compliance Becomes Second Nature
Preparing for a CMMC assessment is ultimately about credibility. Assessors are looking for consistency, traceability and operational maturity, not perfection. A well-structured CMMC compliance guide, supported by thorough CMMC compliance steps and a clearly defined process flow, allows your organization to confidently and continuously present that maturity.
Emily Newton is the Editor-in-Chief at Revolutionized Magazine. A regular contributor to Brilliance Security Magazine, she has over four years of experience writing articles in the industrial sector.
.
.
Additional Resource
Video Overview
Follow Brilliance Security Magazine on LinkedIn to ensure you receive alerts for the most up-to-date security and cybersecurity news and information. BSM is cited as one of Feedspot’s top 10 cybersecurity magazines.


