By Emily Newton, Editor-in-Chief at Revolutionized Magazine
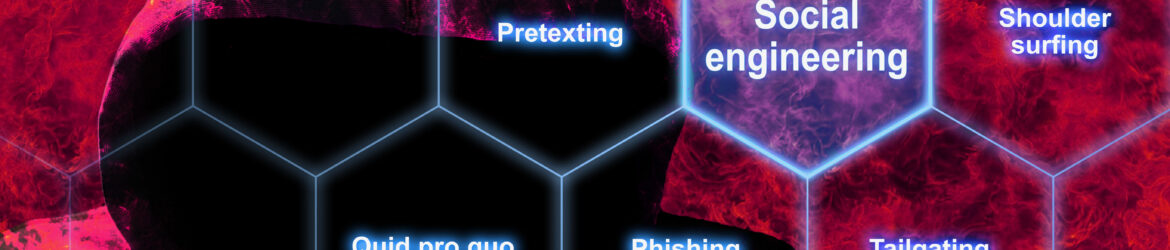
Not every cyberattack comes through software vulnerabilities and secretive server backdoors. Sometimes, social engineering attacks take advantage of human ignorance or misunderstanding, and that’s enough.
Social engineering attacks are rising as threat actors attempt to circumvent bolstered cybersecurity practices through old-fashioned manipulation and information extraction. These attacks get trickier by the day. These are some of the most novel and prevalent — alongside ways to stay resilient in their presence.
1. Watering Hole
Watering holes tempt users because they take on the visage of easily recognizable and trusted webpages. However, hackers discover sites their target visits regularly in advance and infect them with malicious code. These codes sweep the website with harmful software or trojans, or the threat actor secures visitors’ credentials. It’s easy to spy on most web users nowadays, from compromised webcams, extensive browser history and even sticky notes containing sensitive information in workspaces.
Watering hole attacks are ubiquitous to victims yet a product of extensive research from threat actors to discover web trends and personal habits to exploit. It could be a small-business patron or government employee logging into their work email or internet provider domain as usual. They are then deceptively conned into giving up their information.
The most basic cybersecurity hygiene habits can prevent social engineering attacks. Companies and individual employees can:
- Ensure no personal information is in the open, in unprotected digital documents or in physical paper versions.
- Use VPNs to disguise web activity.
- Delete web browsing history.
- Use password managers and ensure passwords aren’t saved within browsers.
- Update operating systems and programs regularly to minimize vulnerabilities.
2. Tailgating
Imagine someone walking into a barred building after scanning a key card. While the gate is open, an unauthorized person takes advantage and walks in with them, gaining access to places they shouldn’t. This is known as tailgating or piggybacking and can happen in digital realms, too. Once they sneak past the barrier, networks, accounts and servers are all in the hands of threat actors.
Attackers may send emails from fake accounts that simulate fellow employees or third-party vendors. These are simple ways hackers can impersonate trustworthy sources to obtain credentials. In-person tailgating attacks can still be a form of social engineering, especially if criminals pose as postal workers or some other service with various personnel — resulting in compromised digital information. Overhearing one conversation could be all they need to perform the intel they need to execute attacks.
Use these tactics to avoid tailgating:
- Question every unfamiliar face with other known staff.
- Check employees for badges or identification, or ask others if they know a name.
- Increase in-person security and digital authentication.
- Check email domain names for inconsistencies, such as misspellings.
- Don’t give personal information in conversations.
- Hide passwords or personal data in open areas.
3. Phishing Variants
Most are familiar with phishing, which is sending corrupt or malicious attachments in emails or other digital communications that transmit viruses or malware. However, it comes in numerous forms as the creativity of hackers skyrockets and new technologies allow them to expand their activities:
- Spear phishing: This is a blend of watering hole research and phishing. These attacks are highly targeted and curated for unique victims.
- Whaling: This includes phishing high-profile, famous or high-class individuals with much to lose.
- Smishing: Also known as SMS phishing, it is email phishing but through text messages.
- Vishing: Vishing uses voice channels to social engineer information out of victims, like through phone calls.
- Angler phishing: This method uses social media channels and fake accounts to swindle personal information from users in direct messages or other modes.
As with other social engineering attacks, employees should be wary of all communications. Cybersecurity teams must ensure strong spam filters and authentication measures in their routing.
4. Pretexting
These social engineering methods are attacks with a theatrical element. Someone may pose as an auditor, or a fraudulent online customer service submission could have people input excessive and unnecessary information. Regardless of the scenario, the social engineering happens via a pretext. Numerous authoritative entities like a hospital or the IRS will have callers verify Social Security numbers, so sometimes employees will freely hand them out to seemingly relevant individuals who are pretexting.
Comprehensive training is one of the most efficient ways to reduce pretexting and all other social engineering attacks. Engage employees in mock scenarios and regular penetration testing to see how they perform in an organic environment. This allows companies to see what employees need specialized attention or deeper awareness.
Companies can also relay to employees business reasons why they may need to provide information and what it will contain. This allows them to know what entities could ask for and what to prepare — anything else in excess could be suspicious.
5. Quid Pro Quo
Threat actors may convince victims to hand over information by convincing them they will get a benefit in return, hence quid pro quo social engineering. This method combines with other tactics, like baiting, which promises tangible rewards instead of quid pro quo services. Bribes could include cash payments or changing information within a database to provide a competitive advantage within the company.
Companies can reduce the number of quid pro quo social engineering attacks by doing the following:
- Hiring employees with verifiable character and diverse references.
- Performing regular check-ins to ensure employee satisfaction, minimizing the risk of deceptive activities.
- Increasing company culture to reduce animosity among employees.
Staying Protecting Against Social Engineering Attacks
Social engineering attacks attempt to gain digital advantages through emotionally driven, intimate tactics that exploit technological naivety. Awareness is the top priority, and taking a moment to second-guess every digital interaction and communication will also help stop countless attacks.
Avoid some of the most damaging in the industry by following these preventive measures. These concrete steps will keep identities and personal information safe from threat actors.
Emily Newton is the Editor-in-Chief at Revolutionized Magazine. A regular contributor to Brilliance Security Magazine, she has over four years of experience writing articles in the industrial sector.
.
.
Follow Brilliance Security Magazine on LinkedIn to ensure you receive alerts for the most up-to-date security and cybersecurity news and information. BSM is cited as one of Feedspot’s top 10 cybersecurity magazines.